LEAKED: How To Level Up In The Future Using Forbidden Techniques!
Have you ever wondered what it would take to push beyond conventional limits and achieve extraordinary results? In a world where everyone follows the same rules, the most powerful breakthroughs often come from techniques that others dare not attempt. Today, we're revealing the secrets of forbidden techniques that can transform your gaming, personal development, and strategic thinking to the next level.
The Forbidden Path to Mastery
For Nick Foster, the infamous underachiever, this is his third awakening exam. Like many of us, Nick has struggled with conventional methods, finding himself stuck in patterns of mediocrity. But what if the key to breaking through isn't working harder within the system, but rather embracing techniques that most would consider too dangerous or unconventional?
The concept of forbidden techniques isn't new. From ancient martial arts traditions to modern gaming strategies, the most powerful methods are often those that come with significant risks. In Naruto, forbidden jutsu offer great power, but also endanger either the user or the world at large. These techniques represent the ultimate paradox: the greatest rewards often require the greatest sacrifices.
- 8 Foot Christmas Tree Gone Nude The Viral Truth About Decorating Disasters
- Movierulz Com 2025 Kannada
The Price of Power
Honestly, I'd love some form of twisted forbidden jujutsu techniques that you can only access by selling your soul and humanity in the process. This dark allure is precisely what makes forbidden techniques so compelling. Think the eaters from First Law trilogy, or Sukuna from Jujutsu Kaisen, who would fit into this category since he does have cannibalistic tendencies.
The psychological appeal is undeniable. When Jiang Ming woke up in a strange world, he learned he had obtained immortality. In the dangerous and ruthless world of cultivation, he was determined to carve his unique path. Taking advantage of his immortality, he vowed to learn forbidden skills that would normally eat away at the user's life. This scenario perfectly illustrates the core principle: when you remove the ultimate limitation (death), you can afford to take risks that others cannot.
Strategic Applications in Gaming
The principles of forbidden techniques extend far beyond fantasy and into practical applications. In Clash of Clans, pushing to legends after an update requires strategies that most players wouldn't consider. It might mean abandoning conventional base designs, experimenting with troop compositions that seem counterintuitive, or timing attacks in ways that defy standard advice.
- Infección Por Levaduras Filtrada El Escándalo Médico Que Ocultan
- The Naked Secret To Perfect Hair For Straight Haired Men Leaked
In space strategy games, all ships tier 2 and above can equip forbidden tech to boost their capabilities. To unlock a ship's forbidden tech slot, you need fusion rods, which can be obtained by exchanging forbidden tech credits in the refinery. This mechanic perfectly mirrors real-world innovation: breakthrough technologies often require rare resources and significant investment.
The Teaching Paradox
A common way to use this trope is for an old master to teach the technique but insist that the hero isn't ready to use it yet. Rule of drama dictates that the hero must keep the technique in their back pocket until such time as they have no choice but to use it. This narrative device reflects a profound truth about forbidden techniques: they're not just about power, but about timing and wisdom.
The master's hesitation isn't just about protecting the student; it's about ensuring they understand when and how to deploy such powerful tools. Using a forbidden technique at the wrong time can be worse than never using it at all. This principle applies equally to business strategies, personal relationships, and life decisions.
Data Security: The Forbidden Knowledge of the Digital Age
What is a data leak? A data leak is an overlooked exposure of sensitive data, either electronically or physically. Data leaks could occur internally or via physical devices such as external hard drives or laptops. If a cybercriminal locates a data leak, they can use the information to arm themselves for a data breach attack.
When sensitive data is stolen from either a data breach or a leak, the consequences can be catastrophic. This represents a modern form of forbidden knowledge – information so powerful that its exposure can destroy organizations and lives. The parallels between mystical forbidden techniques and cybersecurity vulnerabilities are striking: both involve knowledge that can be used for tremendous benefit or devastating harm.
Ethical Considerations and Personal Growth
The pursuit of forbidden techniques raises fundamental questions about ethics and personal growth. Are we willing to sacrifice our principles for power? Can we handle the responsibility that comes with advanced knowledge? These aren't just philosophical questions – they're practical considerations that affect every major decision we make.
Consider the MacBook Neo, now available to preorder. The development of such cutting-edge technology involves pushing boundaries and exploring techniques that were once considered impossible or impractical. The engineers and designers who created it had to make countless decisions about what risks were worth taking and what lines should not be crossed.
Implementation Strategies
How can you apply forbidden technique principles to your own life and work? Here are practical approaches:
Start with Mastery of Fundamentals: Before you can effectively use advanced techniques, you need to understand the basics thoroughly. This foundation allows you to recognize when conventional approaches aren't working.
Identify Your Unique Advantages: Like Jiang Ming's immortality, what special circumstances or resources do you have that others don't? These can be your "fusion rods" – the rare materials needed to unlock forbidden capabilities.
Calculate the Cost-Benefit Ratio: Every forbidden technique comes with a price. Before pursuing one, understand exactly what you're risking and whether the potential reward justifies it.
Timing is Everything: The old master's wisdom about not being "ready" often means you haven't yet encountered the situation that absolutely requires that technique. Patience and preparation are crucial.
Create Safe Testing Environments: Before deploying a forbidden technique in a critical situation, test it in low-stakes scenarios where failure won't be catastrophic.
The Future of Forbidden Techniques
As technology advances and our understanding of the world deepens, what we consider "forbidden" continues to evolve. Techniques that were once impossible become commonplace, while new frontiers of knowledge emerge that challenge our ethical frameworks.
The strongest forbidden techniques aren't necessarily those with the most obvious power, but rather those that require the deepest understanding and wisest application. Whether you're playing Clash of Clans, building a business, or navigating personal challenges, the principles remain the same: extraordinary results require extraordinary approaches, but wisdom determines whether those approaches lead to triumph or tragedy.
Conclusion
The world of forbidden techniques offers a fascinating lens through which to view personal growth, strategic thinking, and ethical decision-making. From the mythical paths of cultivators like Jiang Ming to the practical strategies of modern gamers and cybersecurity professionals, the pursuit of forbidden knowledge continues to drive human advancement.
The key isn't to recklessly pursue every dangerous technique, but rather to understand when conventional approaches have reached their limits and calculated risks become necessary. By studying the principles behind forbidden techniques – their power, their costs, and their proper applications – we can make better decisions about when to push beyond conventional boundaries and when to stay within them.
Remember Nick Foster's journey: sometimes the third attempt is the one that finally breaks through because you've learned enough to recognize which rules are worth breaking. The future belongs to those who can identify the right forbidden techniques for their unique circumstances and have the wisdom to use them appropriately.

Forbidden Techniques
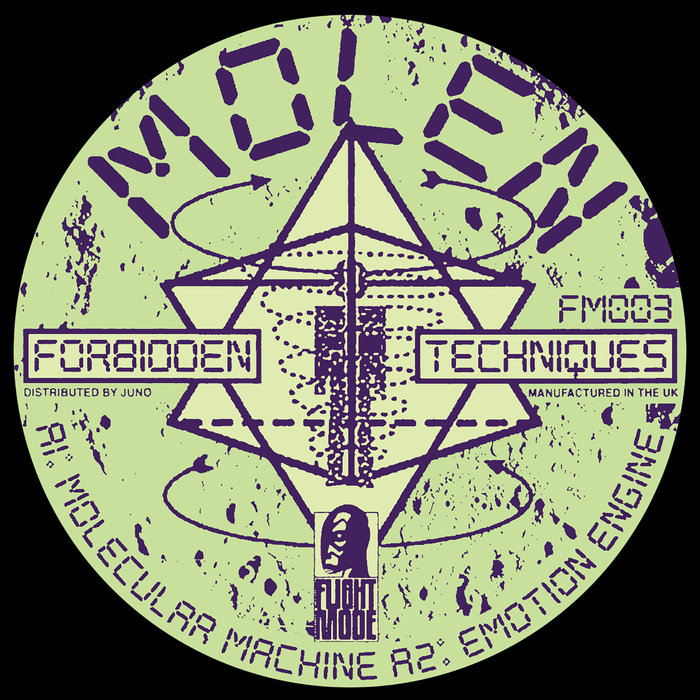
Forbidden Techniques | Molen | Flight Mode

Rumors Swirl Over Leaked Cassidy Battlepass Mythic : LevelUpTalk