The Dark Secret Of 'NVM' Exposed: How It's Destroying Your Texts!
Have you ever noticed how your carefully crafted messages can suddenly disappear or change before your eyes? The mysterious acronym "NVM" might seem harmless at first glance, but what if I told you it's at the center of a digital conspiracy that's silently corrupting our communications? From secret service text disappearances to relationship breakdowns, NVM has become the invisible force reshaping how we interact in the digital age.
The Hidden Threat of Modern Storage Devices
The SSD has been mining for interesting, secret documents, intelligence of any kind, it can silently transfer them to one of the attacker servers. This isn't science fiction – it's the reality of modern cybersecurity threats that most users never see coming.
Beyond simple data theft, these malicious storage devices represent a fundamental breach of trust in our computing infrastructure. The very devices we rely on to store our most precious memories and sensitive information have become potential Trojan horses, silently working against us while appearing completely innocent.
The EnvMe Platform: A New Era of Hardware-Based Threats
In this paper, we challenge this trust by introducing the EnvMe platform, a malicious NVMe storage device. This isn't just another software vulnerability – it's a hardware-level attack that bypasses traditional security measures entirely.
The EnvMe platform features a novel approach to compromising systems at the most fundamental level. By exploiting the trusted relationship between operating systems and storage devices, attackers can gain unprecedented access to sensitive data without triggering conventional security alarms.
- Let That Sink In The Leaked Nude Photos That Destroyed A Career
- Shocking Leak Pepper In Your Salt And Pepper Is Actually Poisoning You
The Trust Gap in Modern Computing
Modern operating systems manage and abstract hardware resources, to ensure efficient execution of user workloads. This abstraction layer is designed to protect users and create a seamless computing experience, but it also creates a false sense of security.
The operating system must securely interface with often untrusted user code while relying on hardware that is assumed to be trustworthy. This assumption represents a critical vulnerability that malicious actors have begun to exploit systematically.
The Technical Underpinnings of Storage Vulnerabilities
By looking at the vulnerable code piece in nvmet_setup_host, we can see that the bug can be triggered if there is a problem in the extraction of the host ctrl auth key, which is done in nvme_auth_extract_key. This technical detail reveals how sophisticated these attacks have become.
NVMe security is an element of the 2.0 specification, yet implementation flaws continue to plague even the most recent security protocols. The complexity of modern storage systems creates numerous attack vectors that can be exploited by determined adversaries.
The Human Impact: Relationships in the Digital Age
How does NVM affect relationships? NVM can have both positive and negative effects on relationships, depending on how it's used and perceived. In an era where digital communication dominates our personal interactions, the reliability and security of our messaging platforms has never been more critical.
When used in a lighthearted or humorous way, NVM can help to diffuse tension or avoid conflict in a relationship. However, when messages disappear or change without explanation, it can create confusion, mistrust, and ultimately damage the foundation of personal connections.
The Cultural Context: Understanding Modern Communication
My mission is to spread awareness about the dark realities of internet culture. The phenomenon of disappearing messages and altered communications represents a broader trend in how we interact online – one that prioritizes convenience over authenticity and security.
This is how brain rot is destroying generation alpha. The constant exposure to unreliable digital communication is shaping how younger generations perceive truth, authenticity, and human connection in ways we're only beginning to understand.
The Broader Implications: Society and Information Integrity
The Dominion voting systems' lawsuit against Fox News didn't go to trial, but still revealed plenty of what Fox personalities, including Tucker Carlson, had been saying about false 2020 election claims. This case highlights how the manipulation of information – whether through deliberate misinformation or technical vulnerabilities – can have profound societal consequences.
His unexplained departure has turned a spotlight on what he said in depositions, emails and text messages among the thousands of pages Dominion. The disappearance or alteration of crucial communications can fundamentally alter the course of legal proceedings, political discourse, and public understanding.
The Ancient Wisdom: Learning from Historical Texts
Ancient texts, sacred texts, Enuma Elish, Emerald Tablet, Book of the Dead, Book of Enoch, more. Throughout human history, the preservation and integrity of written communication has been paramount to cultural survival and knowledge transmission.
For there is nothing hidden that will not be disclosed, and nothing concealed that will not be made known and brought to light. This timeless wisdom reminds us that attempts to manipulate or hide information are ultimately futile, yet the damage done in the interim can be catastrophic.
The Digital Archive: Preserving Truth in an Age of Manipulation
Explore the world's largest free archive of religious, spiritual, and esoteric texts. Over 1700 books on religion, mythology, folklore, Buddhism, Christianity, Islam, Hinduism, and more. These archives represent humanity's collective effort to preserve truth across generations, standing in stark contrast to the ephemeral nature of modern digital communications.
A quiet place in cyberspace devoted to religious tolerance and scholarship. In an age where information can be altered or deleted with a few keystrokes, the importance of permanent, verifiable records becomes increasingly apparent.
The Political Dimension: Power and Information Control
For nearly a month, Farah Griffin acted as an intermediary between Cheney and the select committee. The manipulation of communications and information flow has always been a tool of political power, but digital technologies have amplified both the potential and the risks.
As an intermediary for Cheney, Farah Griffin helped coordinate Hutchinson's third transcribed interview—without Hutchinson's lawyer, Stefan Passantino's knowledge. The unauthorized alteration or disappearance of communications can fundamentally alter the course of investigations and accountability.
During the same time, Farah Griffin and Hutchinson discussed the optics of Hutchinson leaking her "new information" to. The strategic use of information – and the suppression of inconvenient truths – continues to shape our political landscape in ways that often remain hidden from public view.
The Spiritual Dimension: Seeking Truth in a Manipulated World
The Aranyakas, wilderness texts or forest treaties, were composed by people who meditated in the woods as recluses and are the third part of the Vedas. These ancient texts remind us that the pursuit of truth has always required dedication, contemplation, and often, separation from the noise and manipulation of mainstream society.
[40] It is frequently read in secondary literature. The enduring relevance of these ancient wisdom traditions speaks to the universal human need for authentic, unaltered communication and understanding.
The Digital Communities: Finding Connection in Fragmented Spaces
NSFWFantasyTexts is a sub for people who enjoy fantasy text stories, all types of stories are welcome hotwife, cuckold, cheating, M/F, F/F, M/M or whatever you can come up with as long as it is legal. Even in these niche digital communities, the integrity of communication and the ability to trust the medium of exchange remains paramount.
The Investigative Challenge: Uncovering Hidden Truths
There's an investigation now into the mysterious – and maybe criminal – disappearance of the Secret Service's January 6 text messages. When crucial communications vanish without explanation, it undermines public trust and raises serious questions about accountability and transparency.
Why Tucker Carlson's text message about "white men" matters a leaked text that reportedly contributed to Carlson's firing revealed something important about the most racist show on cable. The selective preservation or deletion of communications can dramatically alter public perception and historical record.
The Personal Dimension: Recognizing Warning Signs
Concerned about your partner's texts? Here, therapists share the top 10 texting red flags. In personal relationships, the sudden disappearance or alteration of messages can be a sign of deeper issues, whether technical manipulation or interpersonal problems.
The Academic Response: Preserving Knowledge
OakTrust is Texas A&M University's digital repository for preserving and sharing scholarly works, providing open access to research and academic resources. Academic institutions are increasingly recognizing the importance of creating permanent, verifiable archives in an age of digital ephemerality.
Conclusion: Reclaiming Control in the Digital Age
The dark secret of NVM and its impact on our texts represents just one facet of a much larger challenge facing modern society. As we become increasingly dependent on digital communication, the integrity, reliability, and security of our messaging systems becomes not just a technical concern, but a fundamental requirement for maintaining trust, relationships, and democratic institutions.
The solution lies not in abandoning digital communication, but in developing more robust systems that prioritize authenticity and permanence. We must demand better from the technology companies that control our digital infrastructure, and we must remain vigilant against the subtle ways that information can be manipulated or destroyed.
Most importantly, we must remember that behind every text message, every digital communication, is a human being seeking connection, understanding, and truth. By protecting the integrity of our communications, we protect the very fabric of our shared humanity.
- Shocking Leak Pepper In Your Salt And Pepper Is Actually Poisoning You
- How Old Is Cooking With Kya The Viral Scandal Thats Breaking The Internet
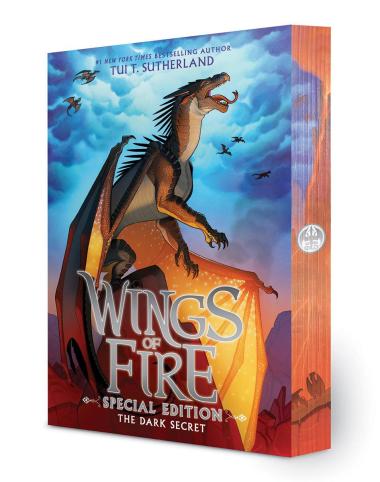
The Dark Secret: Special Edition (Wings of Fire Book Four) | Scholastic

Acne And Gut Health Connection (Exposed Supports Both)

GOUT RESCUE: How To Get Relief From Your Gout In As Little As 2 Hours